Java agent for Glassfish server
For supported agent versions and framework, see APM agents.
Downloading the agent version 1.18.4 (latest)
- Download the agent tar file from the following link.
curl --header "PRIVATE-TOKEN:{{TOKEN}}" --output sixthsense-agent.zip "https://artifacts-observability.sixthsense.rakuten.com/api/v4/projects/4/packages/generic/sixthsense/v1.18.4-latest/agent.zip"
- Copy the tar to the server where Glassfish is deployed and untar the file.
- Delete the tomcat plugin from the agent/plugins directory tomcat-7.x-8.x-plugin-8.5.0.jar.
Configuring the agent
Update the following parameters in the agent.config file in the agent.
- agent.service_name= APPLICATION_NAME
- agent.force_tls= true (For OneCloud Platform use agent.force_tls=${SW_AGENT_FORCE_TLS:false})
- collector.backend_service = URL
- (One Cloud) For connectivity to backend using onecloud private network: 100.99.116.221:80
- (One Cloud) For connectivity to backend using intra public network: 133.237.176.44:80
- agent.authentication = TOKEN_FROM_UI
Configuring on a Glassfish Server
- Add the following entries in the domain.xml file of Glassfish server.
- Make changes in the default and domain1 configurations. It should also be made if you have additional domains configured. The path to the domain.xml file is GLASSFISH_HOME/domain/domain1/config.
-javaagent:/path/to/agent/sixthsense-agent.jar -Xbootclasspath/a:path/to/agent/plugins -Daj.weaving.loadersNotToSkip=ALL -Xverify:none
- Update the following entry in the domain.xml file. Replace with the correct path information in the following configuration.
<jvm-options>-Djava.ext.dirs=${com.sun.aas.javaRoot}/lib/ext${path.separator}${com.sun.aas.javaRoot}/jre/lib/ext${path.separator}${com.sun.aas.instanceRoot}/lib/ext${path.separator}/path/to/agent</jvm-options>
- Modify the osgi.properties file and append the packages. Example: We have appended the org.apache.skywalking.* entry to the list of boot delegation classes.
org.osgi.framework.bootdelegation=${eclipselink.bootdelegation}, \
org.netbeans.lib.profiler, org.netbeans.lib.profiler.*, \
org.apache.skywalking.*
Importing the SixthSense root certificate
SixthSense provides standard root certificates and should be available in most operating system key-stores by default.
However, if Glassfish server is using a separate key-store, perform the following procedure.
- Open the SixthSense backend URL in the browser. The URL is also used in Step 4 of the Agent deployment section (your tenant backend URL)
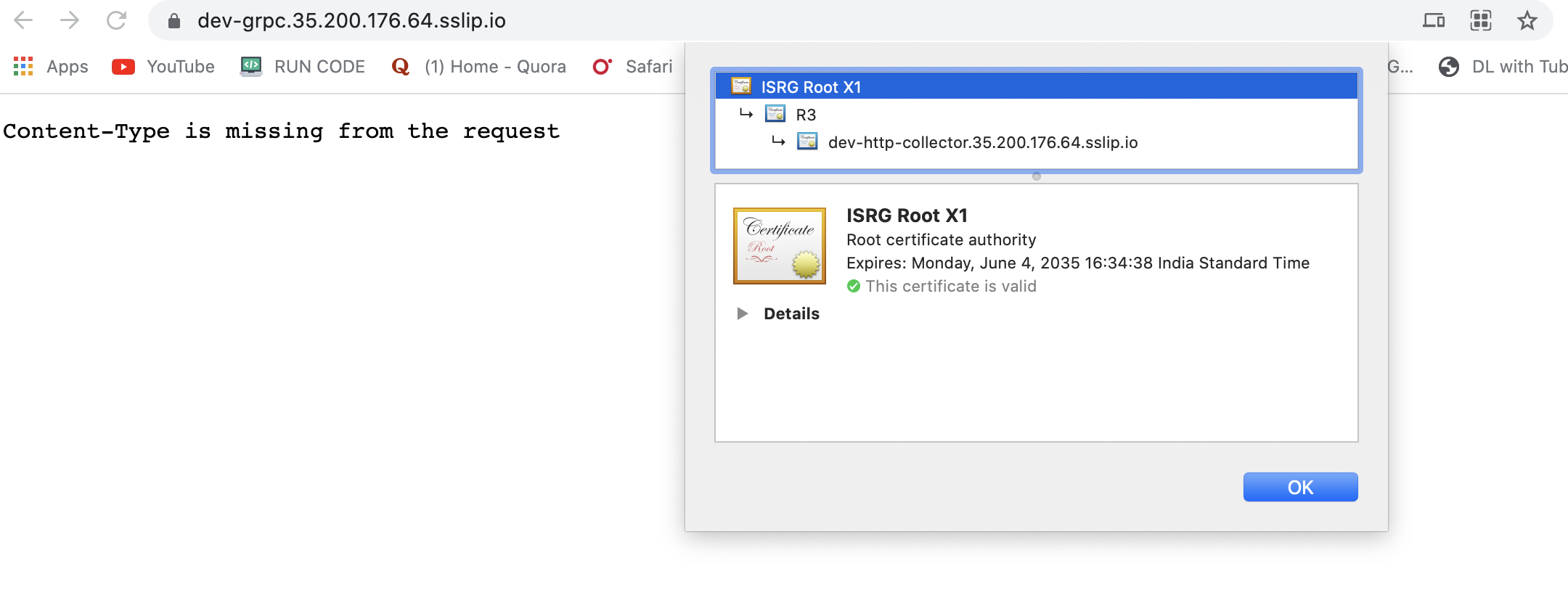
- Click the lock 🔒 icon in the address bar.
- Download the root certificate. In chrome, you can simply drag the Gold colored certificate icon to a directory.
- Copy the ISRG Root X1.cer file to the server where Glassfish is deployed.
- Import the root certificate using the following commands.
# Copy the cert file to a temporary keystore.
keytool -import -trustcacerts -alias root -file ISRG_Root_X1.cer -keystore mykeystore.jks
# Import the certificate to the keystore used by Glassfish server.
keytool -importkeystore -srckeystore mykeystore.jks -destkeystore /path/to/glassfish5/glassfish/domains/domain1/config/cacerts.jks
Support
For any projects in the plugins or support requests, kindly affix the server.log and the agent.log files.